Digital asset security hinges on disciplined controls and clear ownership. Start with strong, unique credentials and enforce layered access with least privilege. Maintain robust backups, continuous monitoring, and ongoing education to detect anomalies. Governance over data, cryptographic standards, and verifiable custody shapes resilience. Threat intelligence informs defenses, yet the pace of change demands ongoing adaptation. The path forward balances usability with protection, leaving unresolved questions about persistent risk and readiness to respond.
What “Digital Asset Security” Really Means
Digital asset security refers to the protective measures, policies, and controls that safeguard digital items—such as passwords, private keys, credentials, and sensitive data—from unauthorized access, theft, or loss. It emphasizes governance of data ownership and adherence to cryptographic standards, ensuring verifiable custody and resilient recovery. A proactive stance identifies risks, enforces least privilege, and documents capabilities, enabling freedom through trusted digital stewardship.
Build Strong, Unique Credentials That Stand Up
Building strong, unique credentials is foundational to digital asset security: it reduces exposure to credential stuffing and phishing, and it constrains attacker movement across systems. The analysis emphasizes disciplined creation and management practices, enabling individuals to maintain autonomy while minimizing risk. A proactive stance ensures credentials stand up under evolving threats, supporting resilient access without sacrificing freedom or usability for legitimate users.
build strong, unique; credentials stand up.
Lock Down Access With Layers and Least Privilege
Locking down access with layered controls and enforcing least privilege reduces the attack surface by limiting each user and process to only the permissions necessary for their role. This approach emphasizes password hygiene and access segmentation, ensuring credentials and tokens are scoped, rotated, and audited. Proactively enforcing policies minimizes risk while preserving freedom to collaborate and innovate within defined boundaries.
Stay Ahead of Threats With Backups, Monitoring, and Education
Backups, monitoring, and education form the triad that keeps digital assets resilient in the face of threats.
A disciplined approach uses backups protocols to ensure data integrity, monitoring dashboards to detect anomalies, and education programs to raise awareness.
Integrating threat intelligence informs proactive defenses, enabling rapid response, continuous improvement, and a freedom-centered posture that anticipates risk without surrendering autonomy.
Frequently Asked Questions
How Often Should I Change My Passwords and PINS?
The frequency of password changes varies by risk, but best practice emphasizes ongoing password hygiene and timely password rotation when exposure or compromise is suspected; routine renewal, coupled with unique credentials, reduces risk while preserving user autonomy and security.
What Two-Factor Methods Balance Security and Convenience?
Two-factor methods, thoughtfully chosen, balance security and convenience. The analyst notes: push notifications and authenticator apps provide prompt, practical protection; hardware keys deliver strong, seamless security with minimal friction. Ultimately, security convenience favors adaptable, user-centric, proactive defense.
Can Hardware Wallets Protect Non-Crypto Digital Assets?
Hardware wallets can protect non cryptocurrency assets by isolating private keys and sensitive metadata, preventing offline exploitation; however, their utility depends on compatible protocols, standardized interfaces, and user-controlled access, ensuring freedom while recognizing limitations in cross-domain compatibility for non cryptocurrency assets.
How Do I Securely Share Access With Trusted Teammates?
Sharing permissions should be granted via role-based access, with time-bound keys and multi-party approval. The approach enables secure collaboration, reduces risk, and preserves freedom by ensuring teammates access only what is necessary, under auditable controls and predefined safeguards.
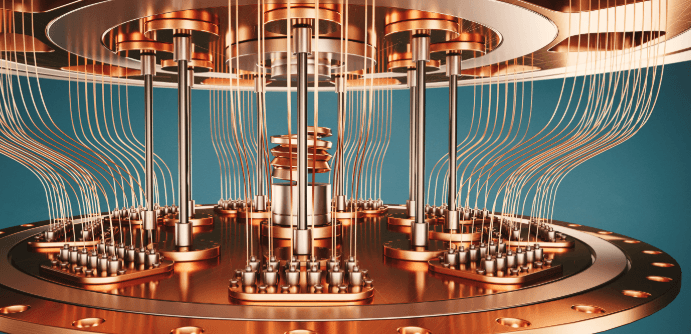
See also: Tech Giants Investing in Quantum
What Indicates a Compromised Device Beyond Obvious Signs?
A compromised device may exhibit unclear indicators and persistent anomalies, according to analysts who emphasize proactive monitoring. The profile suggests irregular traffic, unauthorized software, and credential drift, prompting immediate isolation, thorough forensics, and policy-driven remediation to preserve user freedom.
Conclusion
Digital asset security is best served by disciplined, proactive practices that gently raise the floor of resilience. By cultivating distinctive credentials, enforcing layered access, and embracing routine backups, monitoring, and education, organizations reduce risk without stifling collaboration. This balanced, euphemistic approach preserves usability while nudging defenses upward. With continuous governance, cryptographic diligence, and threat-informed adjustments, the posture remains adaptable and robust, ready to recover gracefully from incidents and to deter evolving, subtle threats before they take hold.